Blog posts (page 2)
-
Turning a Chromebook into a Chrultrabook
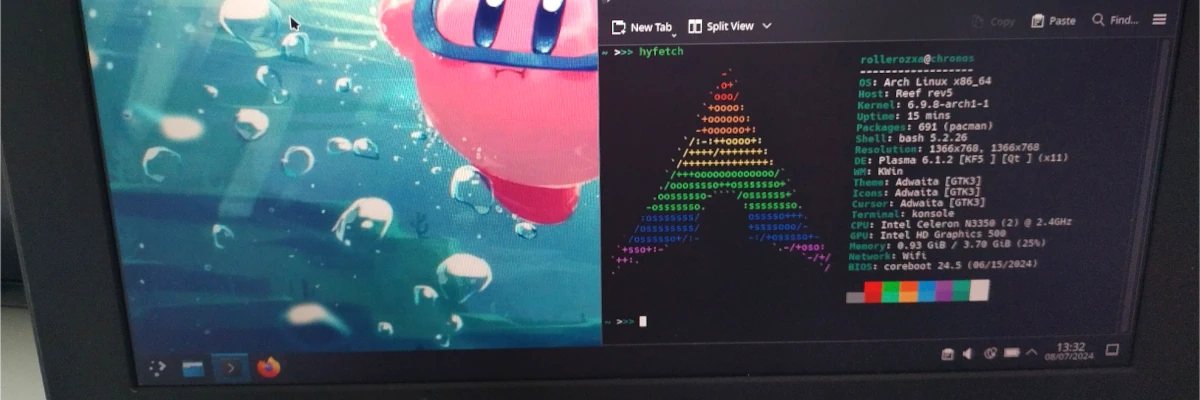
Chromebook is the name of Google's brand of mostly low-end laptops running Chrome OS, an operating system whose primary functionality is running the Google Chrome browser.
When I finished 9th grade and went onto Gymnasiet, I had the option to keep the Chromebook I was given for the past three years at school. Since I had been keeping good care of it for the past years I was using it, why not? I knew that once it gets unlocked I will have access to the containerised Crostini Linux environment, but I was not aware at the time of the ways one can fully install another operating system on it.
-
The History of the Internet
This text was originally written as an assignment about the history of the Internet for my web development course in Gymnasiet during November of 2022. It has been translated from Swedish to English, but the content is preserved in its original state. The Swedish version can be found here.
The Internet has become an essential part of our lives. Accessible via computers, smartphones, and even various ‘smart’ devices such as TVs, fridges or even a smart toaster. But how did we get to this point? And what led to the information age we live in now?
-
Custom Actions in the Dolphin Context Menu
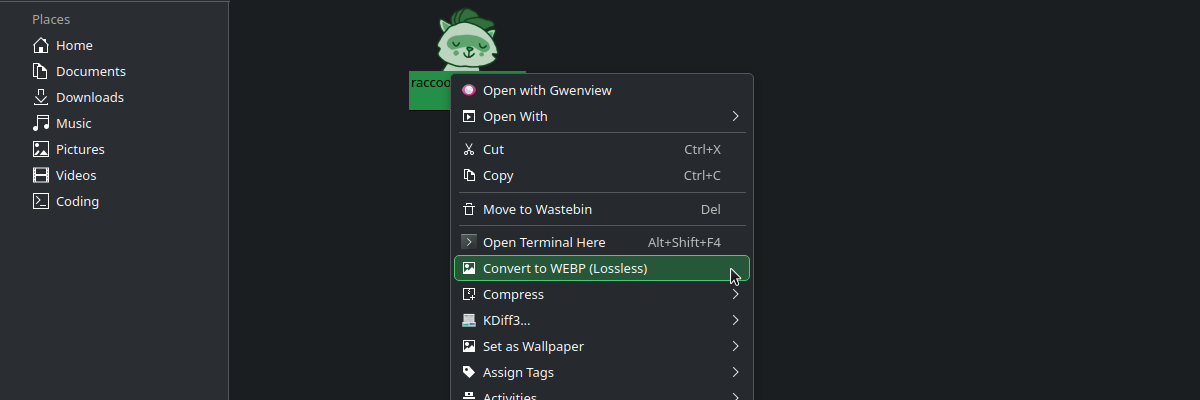
Whenever you right click in Dolphin a context menu appears with a list of various actions you can take depending on the context, if you have selected a particular filetype or a folder. Having not quite yet ascended to the plane of doing all my file management from the terminal, I thought it would be useful to make custom actions for things that I currently do by opening a terminal from Dolphin.
-
Emulating Arch Linux ARM on x86 with QEMU
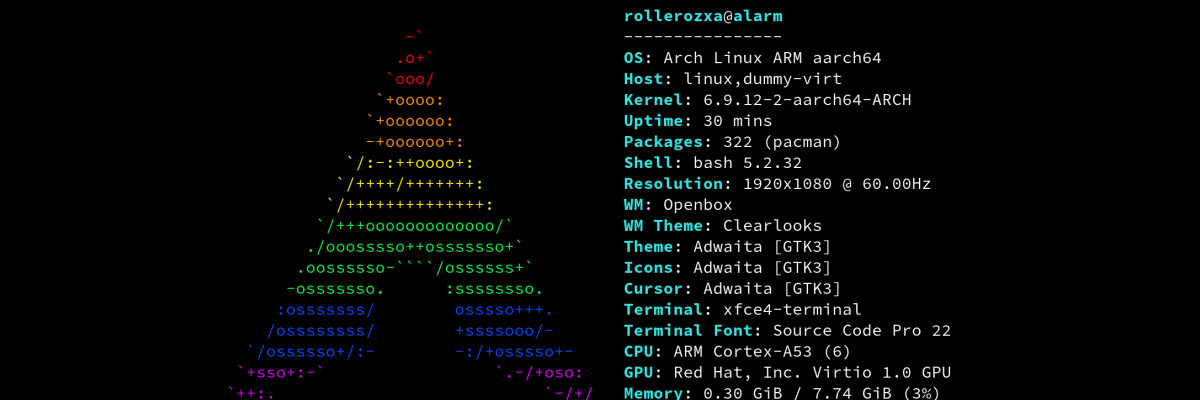
QEMU is usually used for creating virtual machines that operate with the same architecture as the host. However, QEMU is also an emulator that can emulate a wide variety of guest architectures on a host architecture.
Arch Linux ARM is an unofficial flavour porting Arch Linux to ARMv7 and ARMv8, building most packages for ARM and giving you the power of
pacmanto manage packages. -
Archiving the Archive
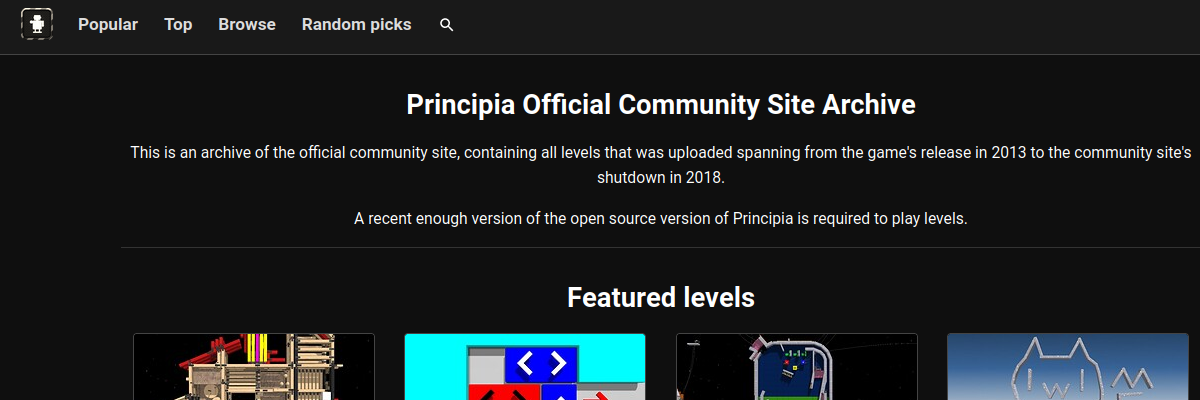
This blog post details my journey as I scraped the entirety of the Principia official community site archive and extracted the data from it to be able to recreate it myself.
-
Washing your Blåhaj

For the past year or so I've been sleeping with a Blåhaj plush. He's big, cute, cuddly and I've loved him ever since I got him. However, throughout the months his face has begun to yellow from rubbing against my face, and just generally becoming a bit dirty. I was scared of washing him because I was worried he would get messed up or deformed by the washing machine, even if IKEA said that he is able to be washed completely fine.
If you're in the same situation as me, don't worry! While his stuffing may become a bit different from before, you can move it around while he's drying and he will hopefully remain just as cute and cuddly as before. Once dried he should return to mostly like how he was before but most importantly, he will be clean!